Validating User Flows to Protect Software Defined Network Environments
Por um escritor misterioso
Last updated 17 dezembro 2024

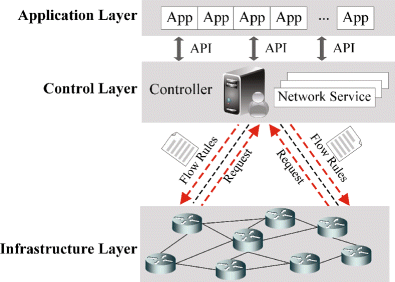
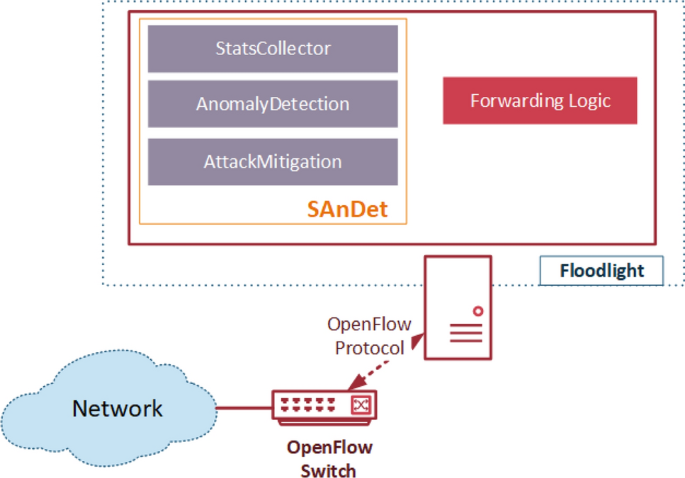
Software Defined Network is a promising network paradigm which has led to several security threats in SDN applications that involve user flows, switches, and controllers in the network. Threats as spoofing, tampering, information disclosure, Denial of Service, flow table overloading, and so on have been addressed by many researchers. In this paper, we present novel SDN design to solve three security threats: flow table overloading is solved by constructing a star topology-based architecture, unsupervised hashing method mitigates link spoofing attack, and fuzzy classifier combined with L1-ELM running on a neural network for isolating anomaly packets from normal packets. For effective flow migration Discrete-Time Finite-State Markov Chain model is applied. Extensive simulations using OMNeT++ demonstrate the performance of our proposed approach, which is better at preserving holding time than are other state-of-the-art works from the literature.
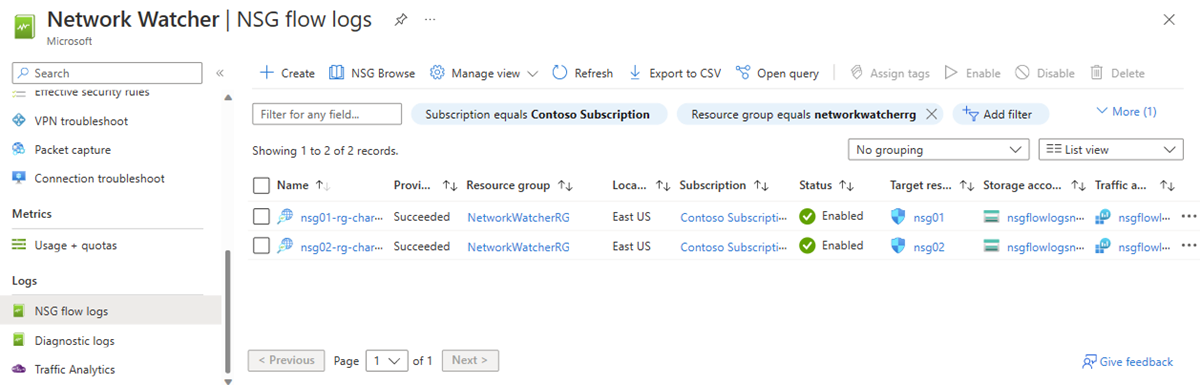
NSG flow logs overview - Azure Network Watcher
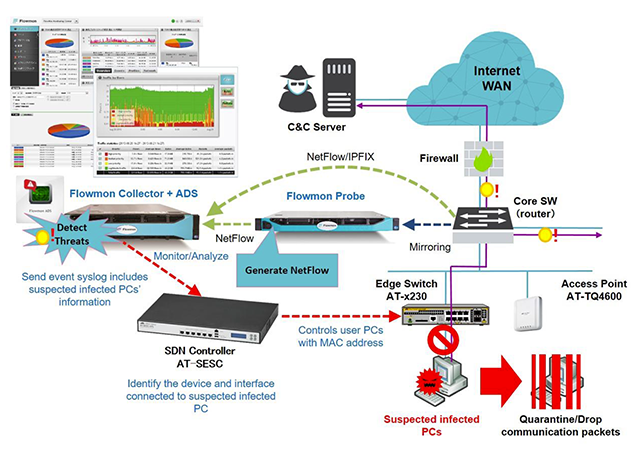
Ensure Security Across Your Entire Network Using Software Defined
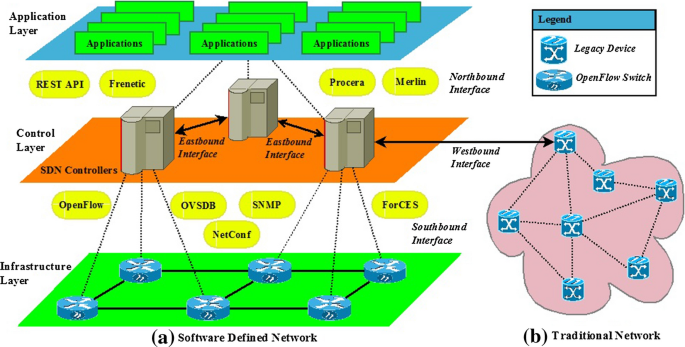
Scalability, Consistency, Reliability and Security in SDN
PERM-GUARD: Authenticating the Validity of Flow Rules in Software
How Netflix uses eBPF flow logs at scale for network insight

Software defined wireless sensor networks application
Flow-based intrusion detection on software-defined networks: a

The application of Software Defined Networking on securing
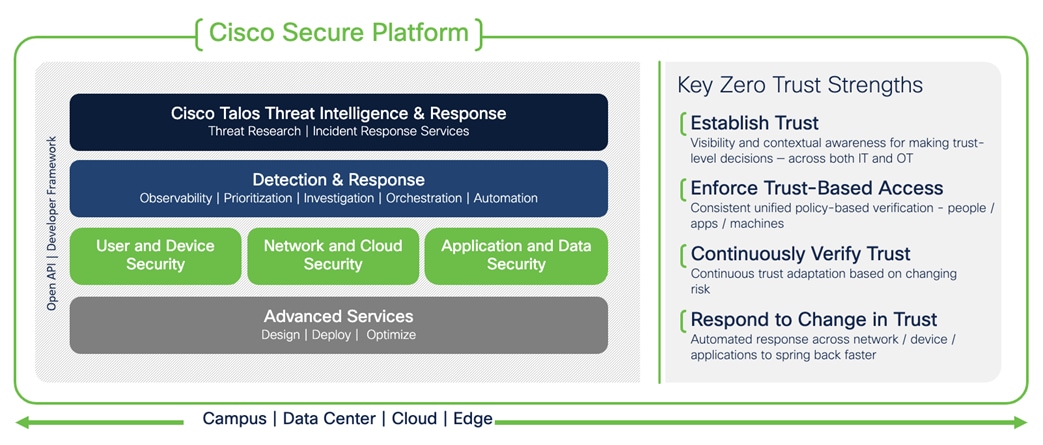
Solutions - Cisco Zero Trust Architecture Guide - Cisco
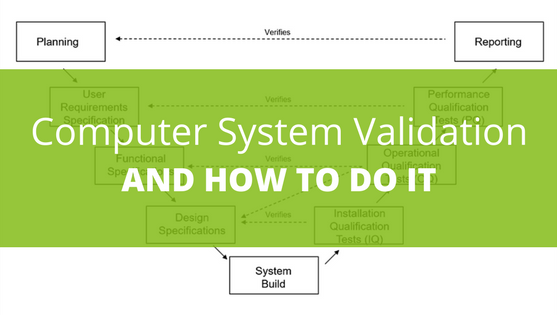
What is Computer System Validation and How Do You Do It?

Validating User Flows to Protect Software Defined Network Environments

What Is Zero Trust Network Access? - Cisco
Recomendado para você
-
5 POO Overloading, PDF, Subroutine17 dezembro 2024
-
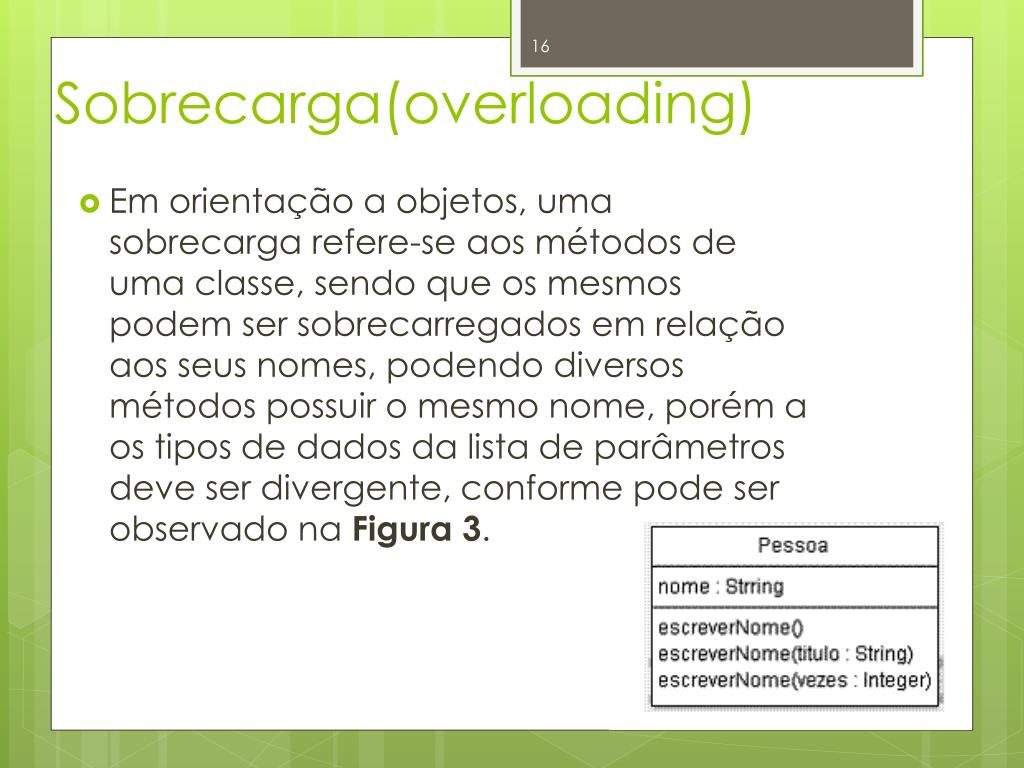 PPT - Programação Orientada à Objetos PowerPoint Presentation, free download - ID:200814417 dezembro 2024
PPT - Programação Orientada à Objetos PowerPoint Presentation, free download - ID:200814417 dezembro 2024 -
Miscelânea: Arrays e Overloading.17 dezembro 2024
-
 Winnie the pooh diaper bag Diaper bag set, Bags, Winnie the pooh17 dezembro 2024
Winnie the pooh diaper bag Diaper bag set, Bags, Winnie the pooh17 dezembro 2024 -
 Coimbatore: Overloaded truck causes road to cave in at flower market17 dezembro 2024
Coimbatore: Overloaded truck causes road to cave in at flower market17 dezembro 2024 -
 Graphical User Interface of POO SG.17 dezembro 2024
Graphical User Interface of POO SG.17 dezembro 2024 -
 Diarrhea in dogs: causes, treatments, and recommendations - 1st Choice Canada17 dezembro 2024
Diarrhea in dogs: causes, treatments, and recommendations - 1st Choice Canada17 dezembro 2024 -
 Social Media Overload Stock Illustrations – 965 Social Media Overload Stock Illustrations, Vectors & Clipart - Dreamstime17 dezembro 2024
Social Media Overload Stock Illustrations – 965 Social Media Overload Stock Illustrations, Vectors & Clipart - Dreamstime17 dezembro 2024 -
 Fecal impaction, Radiology Reference Article17 dezembro 2024
Fecal impaction, Radiology Reference Article17 dezembro 2024 -
 News The Earlsfield Practice17 dezembro 2024
News The Earlsfield Practice17 dezembro 2024
você pode gostar
-
 WWE WrestleMania 39: What To Expect in Los Angeles17 dezembro 2024
WWE WrestleMania 39: What To Expect in Los Angeles17 dezembro 2024 -
 God of War PSP traduzido em português17 dezembro 2024
God of War PSP traduzido em português17 dezembro 2024 -
 REVIEW: Angels of Death E8: Rise - Grimdark Magazine17 dezembro 2024
REVIEW: Angels of Death E8: Rise - Grimdark Magazine17 dezembro 2024 -
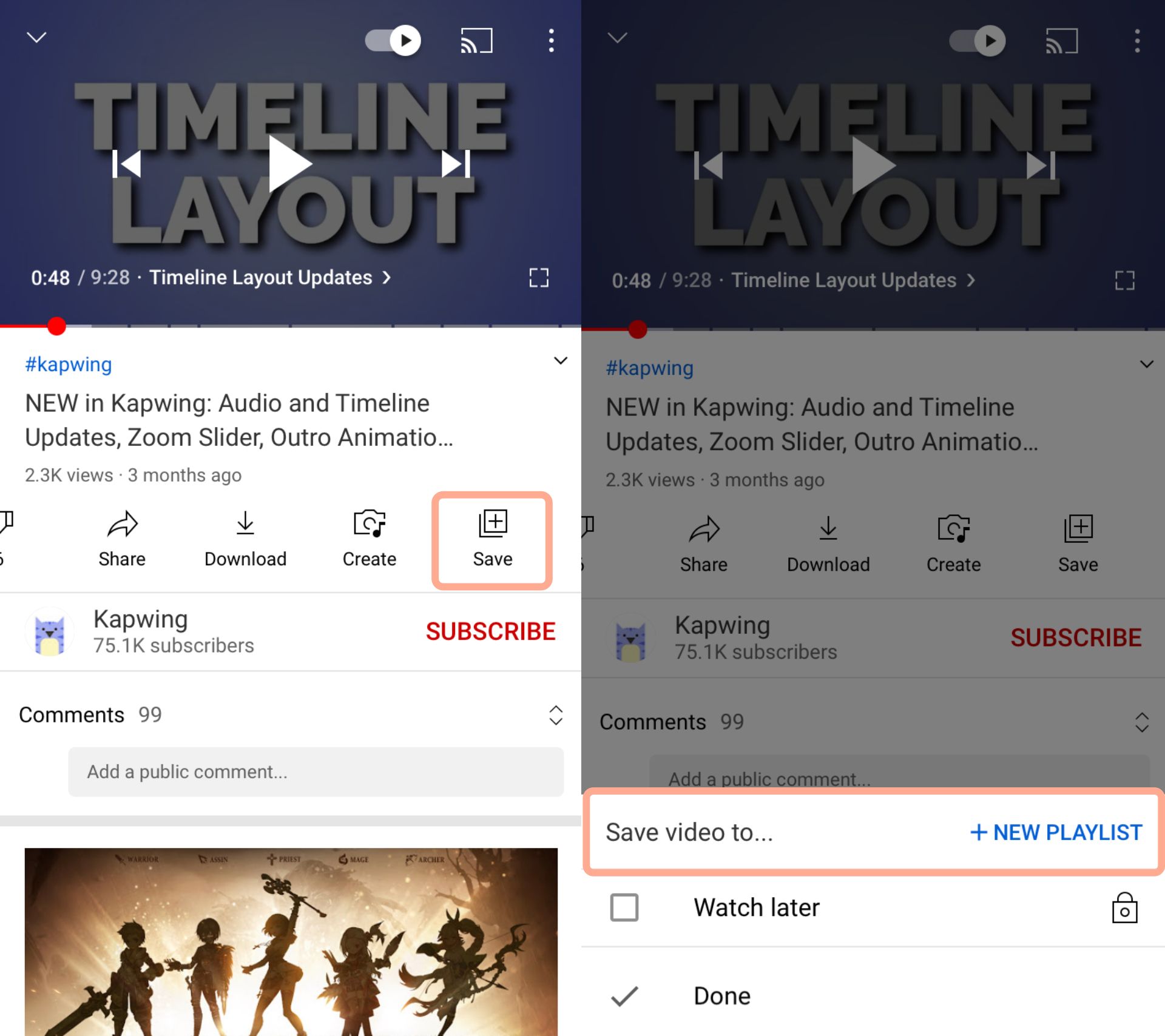 How to Make a Video Repeat17 dezembro 2024
How to Make a Video Repeat17 dezembro 2024 -
classroom of elite season 2 ep 12|TikTok Search17 dezembro 2024
-
 Pokémon Go night and day spawns explained17 dezembro 2024
Pokémon Go night and day spawns explained17 dezembro 2024 -
 Hunter x Hunter 1999 vs 2011 : r/HunterXHunter17 dezembro 2024
Hunter x Hunter 1999 vs 2011 : r/HunterXHunter17 dezembro 2024 -
 Casas Pré Fabricadas - MGF Imóveis - MGF Imóveis17 dezembro 2024
Casas Pré Fabricadas - MGF Imóveis - MGF Imóveis17 dezembro 2024 -
 Blizzard revela 1º personagem gay de 'Overwatch' - Olhar Digital17 dezembro 2024
Blizzard revela 1º personagem gay de 'Overwatch' - Olhar Digital17 dezembro 2024 -
 Judit Polgár's perfect weekend17 dezembro 2024
Judit Polgár's perfect weekend17 dezembro 2024


