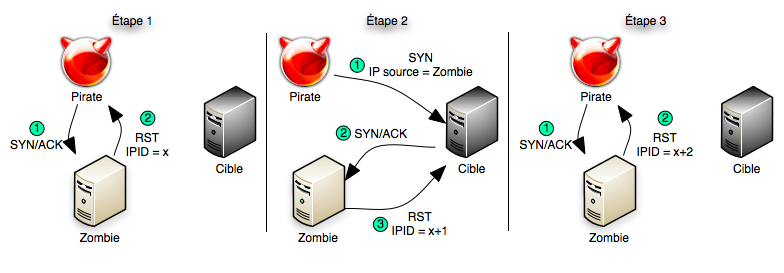
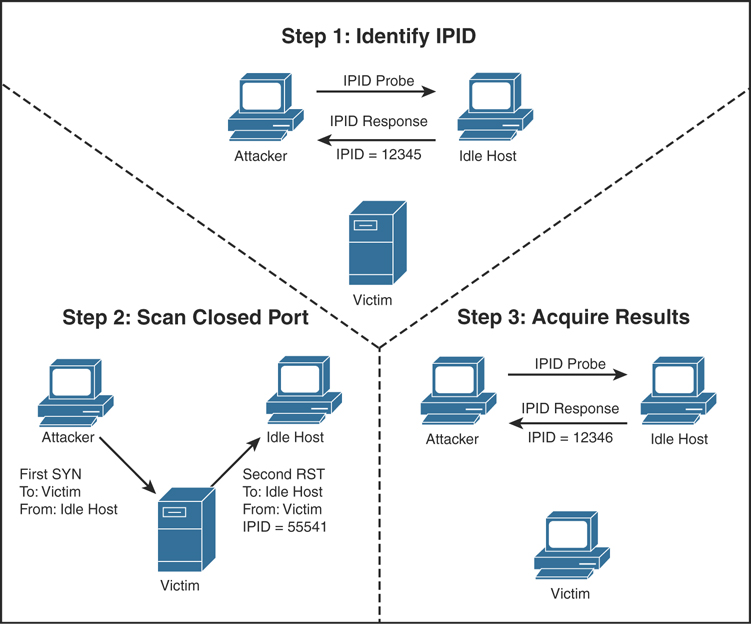
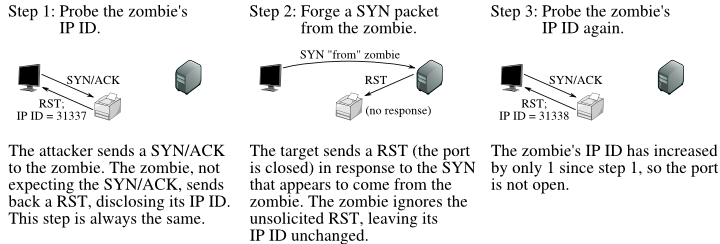
How hackers use idle scans in port scan attacks
Por um escritor misterioso
Last updated 21 setembro 2024
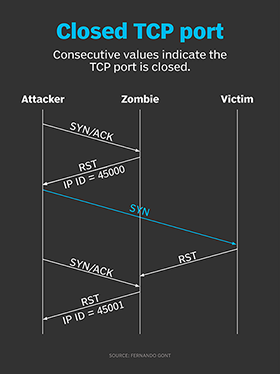
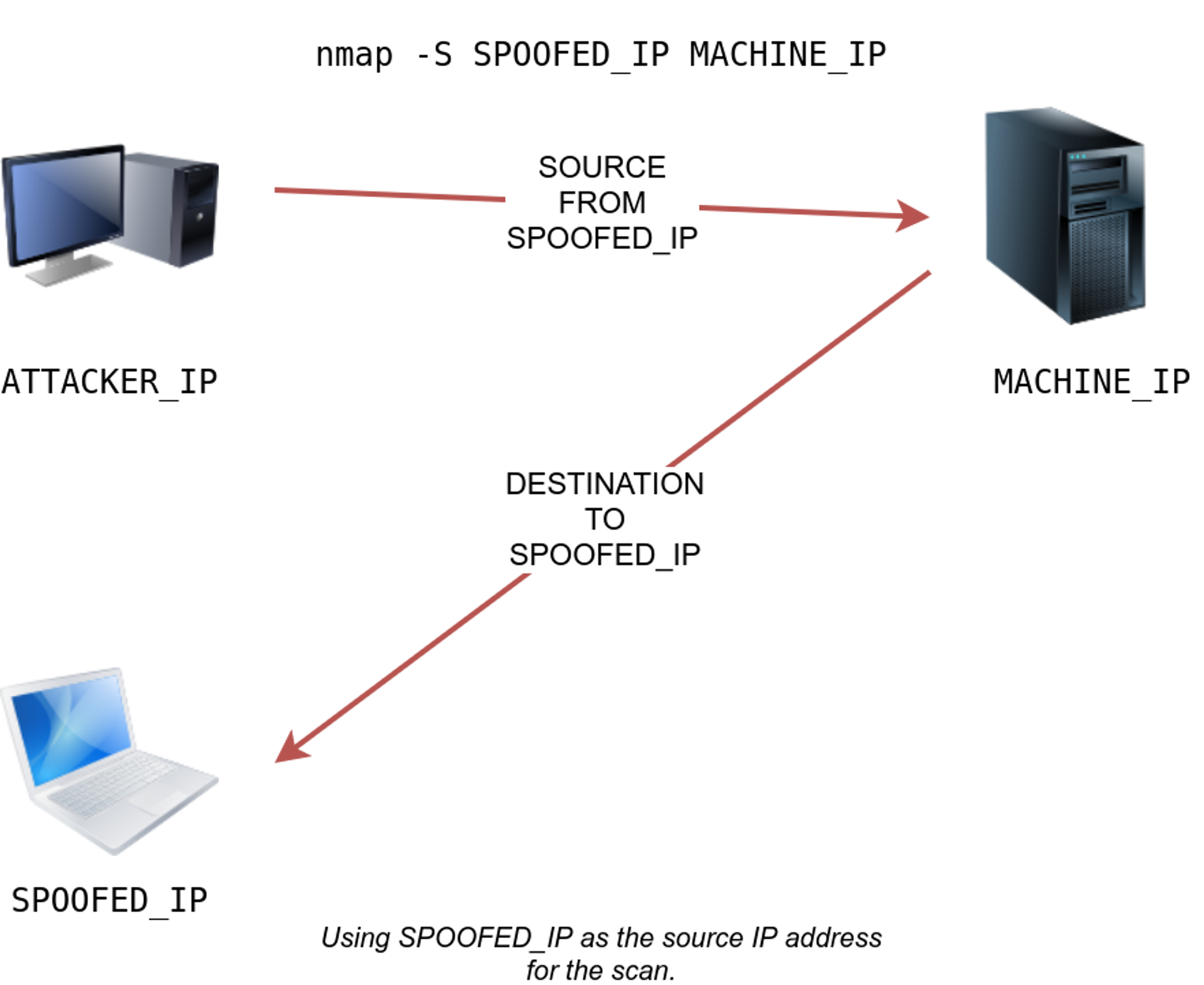
Hackers employ a variety of port scan attacks to gain entry into an enterprise network. Idle scans are a popular method to mask the hacker
Hackers exploit port scan attacks to mask their identities before launching an attack. One of their favorites: the idle scan.
Hackers exploit port scan attacks to mask their identities before launching an attack. One of their favorites: the idle scan.

What is Idle Scan? ICterra Information and Communication Technologies

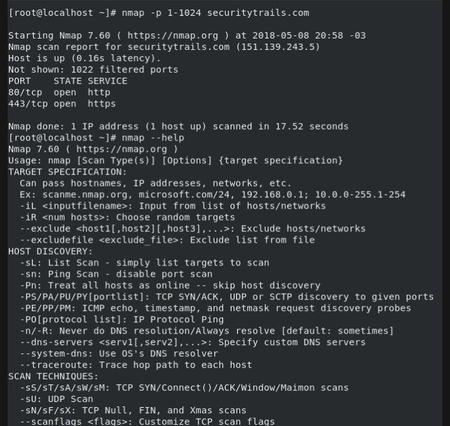
A Complete Guide to Nmap, Nmap Tutorial

Nmap – How to Use Nmap – Spyboy blog
Idle scan - Wikipedia
Scanning, Footprinting, Reconnaissance, and Scanning
TCP Idle Scan (-sI) Nmap Network Scanning

Port Scanning Tutorial for Hackers - Basics

How hackers use idle scans in port scan attacks
What Is Nmap? A Comprehensive Tutorial For Network Mapping
PDF) Port Scanning: Techniques, Tools and Detection

Port Scanning - an overview
The Ultimate Guide to Port Scanning using Nmap
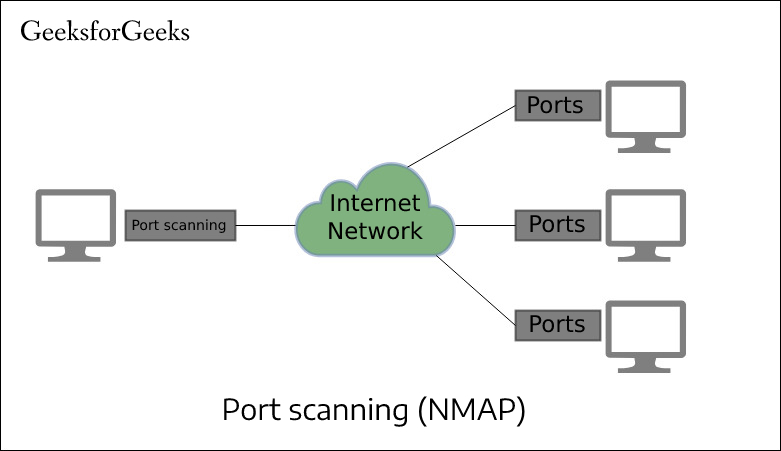
Port Scan in Ethical Hacking - GeeksforGeeks
Recomendado para você
-
 What does your IP address say about you? - CNET21 setembro 2024
What does your IP address say about you? - CNET21 setembro 2024 -
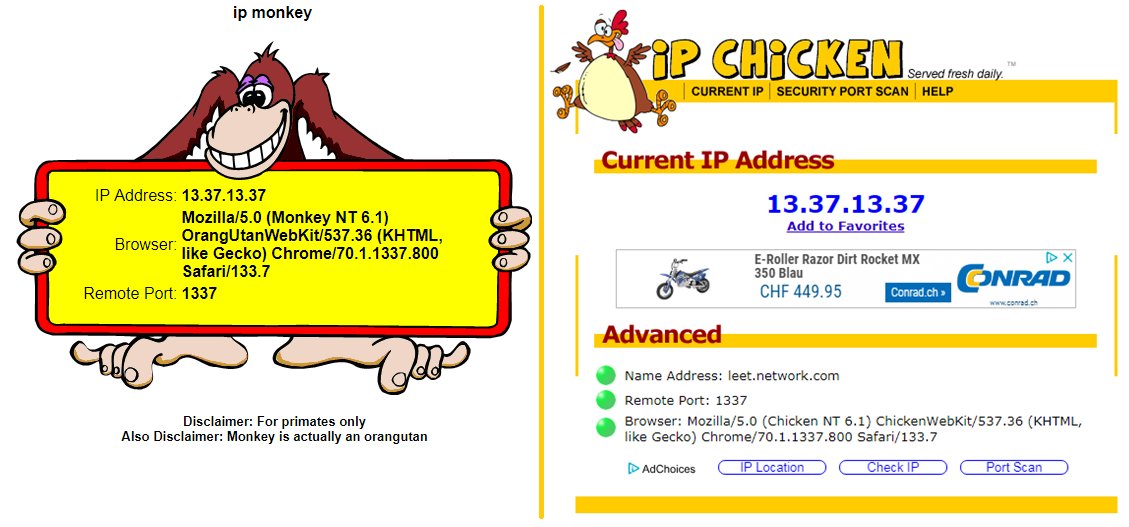 Pascal Gujer on X: / : not only showing your remote IP but also your remote port #ipchicken #ipmonkey #identification deanonymize within carrier-grade natted networks :sigh: / X21 setembro 2024
Pascal Gujer on X: / : not only showing your remote IP but also your remote port #ipchicken #ipmonkey #identification deanonymize within carrier-grade natted networks :sigh: / X21 setembro 2024 -
 IP Chicken - What is my IP address Free public IP lookup21 setembro 2024
IP Chicken - What is my IP address Free public IP lookup21 setembro 2024 -
 like ip chicken 🐔🐔🐔 Ip chicken, Smart city, Coding21 setembro 2024
like ip chicken 🐔🐔🐔 Ip chicken, Smart city, Coding21 setembro 2024 -
 Cyber portfolio21 setembro 2024
Cyber portfolio21 setembro 2024 -
![Zscaler- Source IP Anchoring [SIPA]](https://i.ytimg.com/vi/ylt74TZnS2Q/hq720.jpg?sqp=-oaymwE7CK4FEIIDSFryq4qpAy0IARUAAAAAGAElAADIQj0AgKJD8AEB-AH-CIAC0AWKAgwIABABGDwgEyh_MA8=&rs=AOn4CLAOEq5hhRYj-Kw0ehVImE5Q4ZxLDQ) Zscaler- Source IP Anchoring [SIPA]21 setembro 2024
Zscaler- Source IP Anchoring [SIPA]21 setembro 2024 -
 Top 5 Most Popular Port Scanners in CyberSecurity21 setembro 2024
Top 5 Most Popular Port Scanners in CyberSecurity21 setembro 2024 -
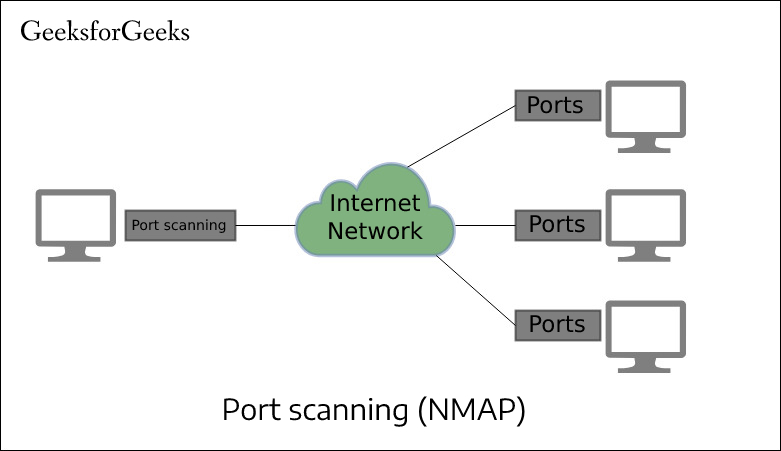 Port Scan in Ethical Hacking - GeeksforGeeks21 setembro 2024
Port Scan in Ethical Hacking - GeeksforGeeks21 setembro 2024 -
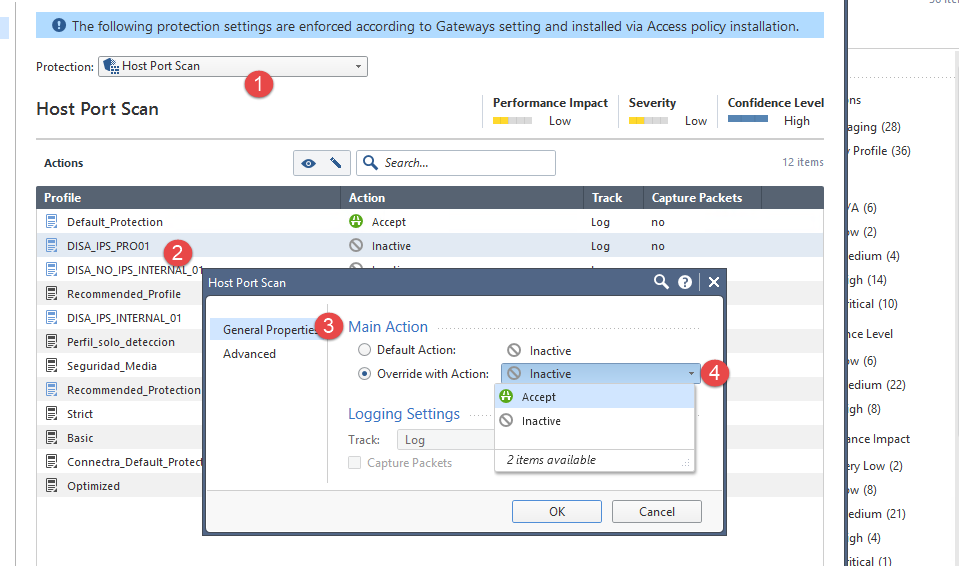 How can I avoid Host Port scan? - Check Point CheckMates21 setembro 2024
How can I avoid Host Port scan? - Check Point CheckMates21 setembro 2024 -
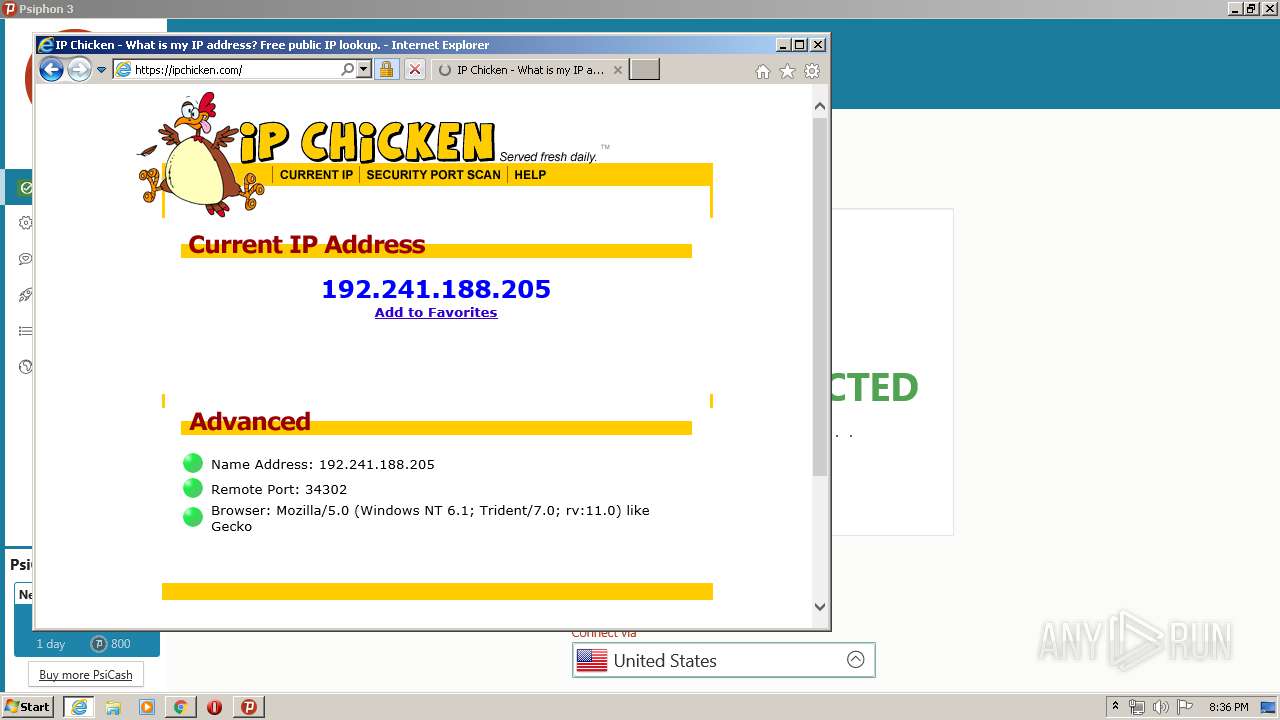 Malware analysis Malicious activity21 setembro 2024
Malware analysis Malicious activity21 setembro 2024
você pode gostar
-
 Penguin Diner 2: My Restaurant Achievements - Google Play21 setembro 2024
Penguin Diner 2: My Restaurant Achievements - Google Play21 setembro 2024 -
Monitor 360hz em Oferta21 setembro 2024
-
 Fan Casting Dove Cameron as Rapunzel in Tangled (Live Action Remake) on myCast21 setembro 2024
Fan Casting Dove Cameron as Rapunzel in Tangled (Live Action Remake) on myCast21 setembro 2024 -
 10 Mind-Blowing Mods That Turn Fallout 3 Into Fallout 4 – Page 921 setembro 2024
10 Mind-Blowing Mods That Turn Fallout 3 Into Fallout 4 – Page 921 setembro 2024 -
 Desenho Para Colorir médico - Imagens Grátis Para Imprimir - img 1211821 setembro 2024
Desenho Para Colorir médico - Imagens Grátis Para Imprimir - img 1211821 setembro 2024 -
 US Air Force Fields New Sniper Rifle Replacement21 setembro 2024
US Air Force Fields New Sniper Rifle Replacement21 setembro 2024 -
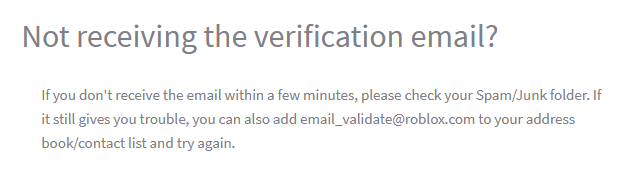 List of Roblox emails, Roblox Wiki21 setembro 2024
List of Roblox emails, Roblox Wiki21 setembro 2024 -
🔸️POKE TRADE CCP🔸️ (@poketrade.ccp) • Instagram photos and videos21 setembro 2024
-
Taylor Swift Jesus T Pose21 setembro 2024
-
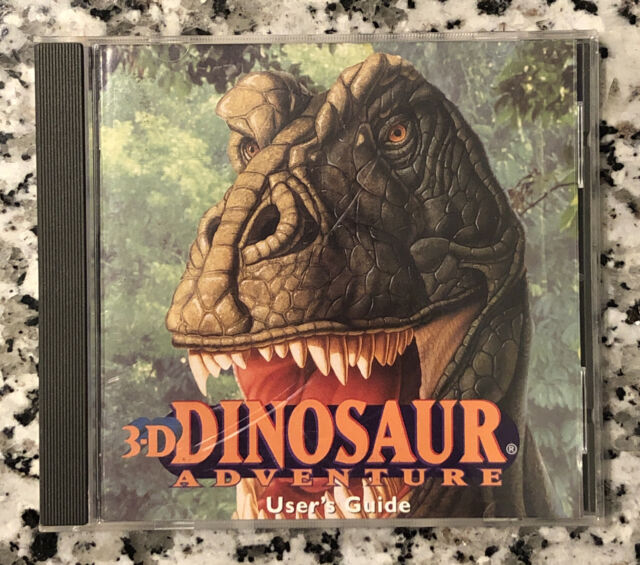 Preços baixos em 3d Aventura de Dinossauros21 setembro 2024
Preços baixos em 3d Aventura de Dinossauros21 setembro 2024


