PDF] Power Consumption-based Detection of Sabotage Attacks in
Por um escritor misterioso
Last updated 21 setembro 2024
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://d3i71xaburhd42.cloudfront.net/d81c8d2816032b4abc1798383f88d5a376d17a75/4-Figure1-1.png)
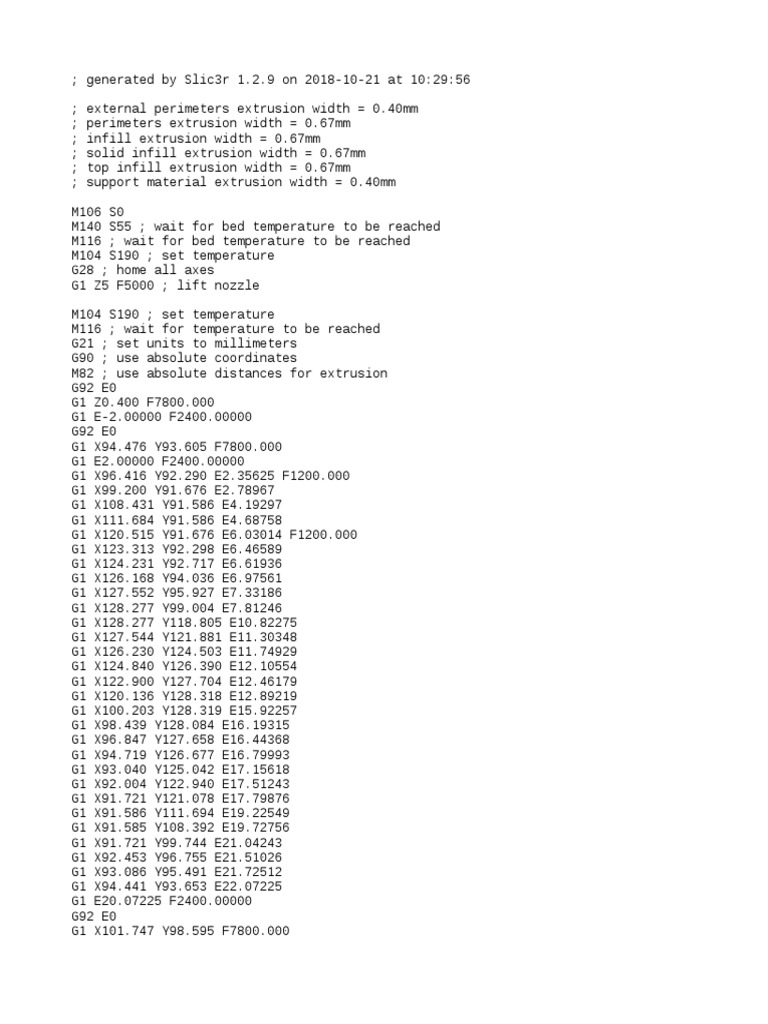
This work proposes a novel approach for detecting sabotage attacks in additive Manufacturing, based on continuous monitoring of the current delivered to all actuators during the manufacturing process and detection of deviations from a provable benign process. Additive Manufacturing (AM), a.k.a. 3D Printing, is increasingly used to manufacture functional parts of safety-critical systems. AM's dependence on computerization raises the concern that the AM process can be tampered with, and a part's mechanical properties sabotaged. This can lead to the destruction of a system employing the sabotaged part, causing loss of life, financial damage, and reputation loss. To address this threat, we propose a novel approach for detecting sabotage attacks. Our approach is based on continuous monitoring of the current delivered to all actuators during the manufacturing process and detection of deviations from a provable benign process. The proposed approach has numerous advantages: (i) it is non-invasive in a time-critical process, (ii) it can be retrofitted in legacy systems, and (iii) it is airgapped from the computerized components of the AM process, preventing simultaneous compromise. Evaluation on a desktop 3D Printer detects all attacks involving a modification of X or Y motor movement, with false positives at 0%.
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://media.licdn.com/dms/image/D5622AQGDAgD1PaMQkA/feedshare-shrink_2048_1536/0/1692244400400?e=1704931200&v=beta&t=kcHoyCYqrFLbp4CuTkFuI4T-Me1TpQ5_vAdkG23noZ4)
Rashedul Islam on LinkedIn: #cybercrime #cybersecurity #mitm #cyberarmy #networksecurity
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://d3i71xaburhd42.cloudfront.net/d81c8d2816032b4abc1798383f88d5a376d17a75/15-Figure11-1.png)
PDF] Power Consumption-based Detection of Sabotage Attacks in Additive Manufacturing
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://engineering.jhu.edu/magazine/wp-content/uploads/2022/05/carousel-3.jpg)
Thwarting Cyberattacks - JHU Engineering Magazine
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://pub.mdpi-res.com/computers/computers-12-00256/article_deploy/html/images/computers-12-00256-g004.png?1702023398)
Computers, Free Full-Text
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://d3i71xaburhd42.cloudfront.net/d81c8d2816032b4abc1798383f88d5a376d17a75/10-Figure5-1.png)
PDF] Power Consumption-based Detection of Sabotage Attacks in Additive Manufacturing
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://media.springernature.com/m685/springer-static/image/art%3A10.1038%2Fs41598-023-45065-8/MediaObjects/41598_2023_45065_Fig1_HTML.png)
IoT empowered smart cybersecurity framework for intrusion detection in internet of drones
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://onlinelibrary.wiley.com/cms/asset/53a07170-5d15-45af-a32b-5f3823379ba6/ett3677-fig-0003-m.jpg)
An overview of security and privacy in smart cities' IoT communications - Al‐Turjman - 2022 - Transactions on Emerging Telecommunications Technologies - Wiley Online Library
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://img.yumpu.com/24279199/1/500x640/comparing-insider-it-sabotage-and-espionage-a-model-cert.jpg)
Comparing Insider IT Sabotage and Espionage: A Model - Cert
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://media.springernature.com/m685/springer-static/image/art%3A10.1186%2Fs42400-019-0038-7/MediaObjects/42400_2019_38_Fig2_HTML.png)
Survey of intrusion detection systems: techniques, datasets and challenges, Cybersecurity
Recomendado para você
-
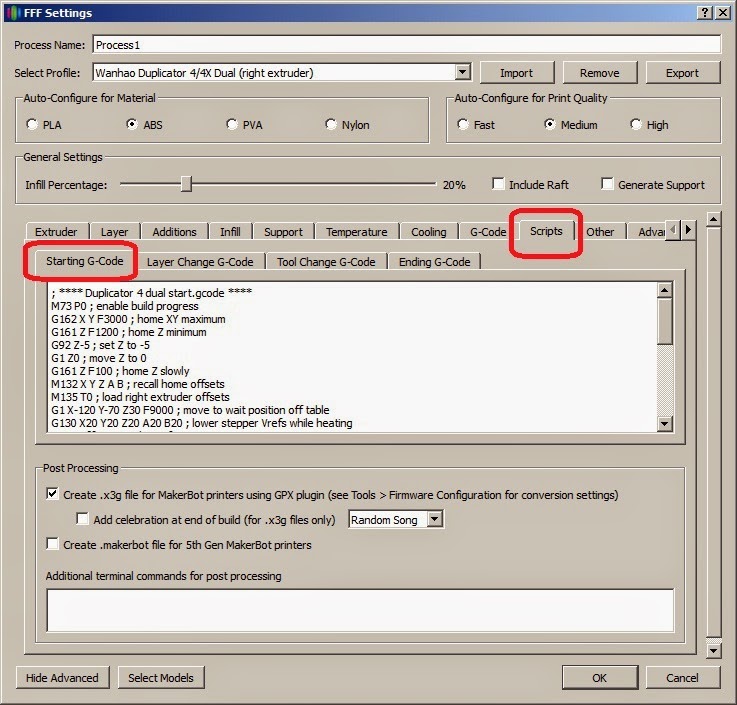 Simplify3d and Duplicator 4. Bed calibration21 setembro 2024
Simplify3d and Duplicator 4. Bed calibration21 setembro 2024 -
 DeskProto user forum21 setembro 2024
DeskProto user forum21 setembro 2024 -
 G1 - Primeiras impressões: BMW R 1200 GS Adventure - notícias em Motos21 setembro 2024
G1 - Primeiras impressões: BMW R 1200 GS Adventure - notícias em Motos21 setembro 2024 -
 Cura 2.4 and Post Processing Scripts? - UltiMaker Cura - UltiMaker21 setembro 2024
Cura 2.4 and Post Processing Scripts? - UltiMaker Cura - UltiMaker21 setembro 2024 -
20mm Calibration Cube, PDF, Alternative Energy21 setembro 2024
-
 A Variety of Observations and Complaints - Bambu Lab X1 Series21 setembro 2024
A Variety of Observations and Complaints - Bambu Lab X1 Series21 setembro 2024 -
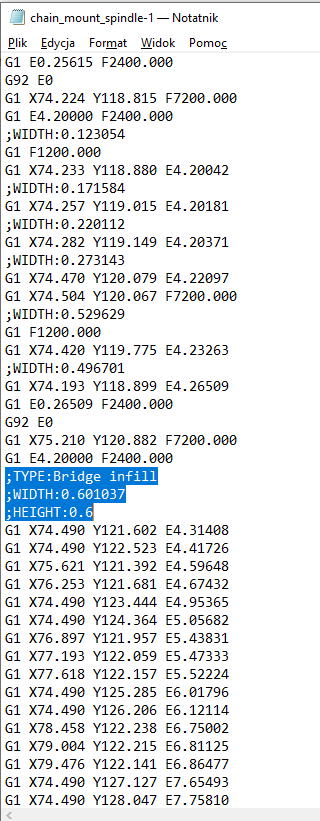 Bridge infill HUGE overextrusion. – PrusaSlicer – Prusa3D Forum21 setembro 2024
Bridge infill HUGE overextrusion. – PrusaSlicer – Prusa3D Forum21 setembro 2024 -
 Weird Circle In G-Code - Bambu Lab Software - Bambu Lab Community21 setembro 2024
Weird Circle In G-Code - Bambu Lab Software - Bambu Lab Community21 setembro 2024 -
 G1 - BMW nacionaliza a R 1200 GS e preço baixa para R$ 69.900 - notícias em Motos21 setembro 2024
G1 - BMW nacionaliza a R 1200 GS e preço baixa para R$ 69.900 - notícias em Motos21 setembro 2024 -
 The 3DCP-SIT system: (a) installation of the SIA on the printing nozzle21 setembro 2024
The 3DCP-SIT system: (a) installation of the SIA on the printing nozzle21 setembro 2024
você pode gostar
-
 Pixel Alliance - Gameplay Android21 setembro 2024
Pixel Alliance - Gameplay Android21 setembro 2024 -
 No! PS5 Does NOT Deserve Hellblade 2!21 setembro 2024
No! PS5 Does NOT Deserve Hellblade 2!21 setembro 2024 -
 Mickey Rourke (younger) vs “Alaric Saltzman” : r/TheVampireDiaries21 setembro 2024
Mickey Rourke (younger) vs “Alaric Saltzman” : r/TheVampireDiaries21 setembro 2024 -
 My Hero Academia: Every Main Characters Signature Move, Ranked21 setembro 2024
My Hero Academia: Every Main Characters Signature Move, Ranked21 setembro 2024 -
 Mommy Long Legs Plush 30 75 Cm Poppy Playtime Plush - Canada in 202321 setembro 2024
Mommy Long Legs Plush 30 75 Cm Poppy Playtime Plush - Canada in 202321 setembro 2024 -
 Pintura Dos Desenhos Animados, Ovos De Doodle, criança, pintado21 setembro 2024
Pintura Dos Desenhos Animados, Ovos De Doodle, criança, pintado21 setembro 2024 -
 Heroes of the Storm (Top 3) - Assassin Patch 17.4 (HotS Tier List21 setembro 2024
Heroes of the Storm (Top 3) - Assassin Patch 17.4 (HotS Tier List21 setembro 2024 -
 CCTV Camera Hacker Simulator for Android21 setembro 2024
CCTV Camera Hacker Simulator for Android21 setembro 2024 -
 Should Blade of Olympus and Exile Return?21 setembro 2024
Should Blade of Olympus and Exile Return?21 setembro 2024 -
a onde assistir 3 temporada de demon slayer|TikTok Search21 setembro 2024